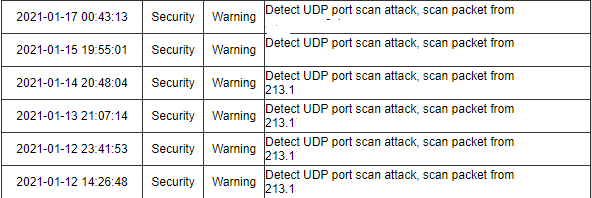
External Attacks: Port Scan_Security Technologies and Applications_Best Practices_Host Security Checks_Hosts Security Issues_Huawei Cloud

Port scan attack successfully blocked through P4. Fig. 5: Scalability... | Download Scientific Diagram

Three UK - our networks are relied upon by the NHS, critical services and you. please take the time to read this 👇and help us protect the UK's critical infrastructure alongside O2

Three UK - our networks are relied upon by the NHS, critical services and you. please take the time to read this 👇and help us protect the UK's critical infrastructure alongside O2

Detecting UDP-based Amplification Attacks_Security Technologies and Applications_Best Practices_UDP-based Amplification Attack Check_Huawei Cloud
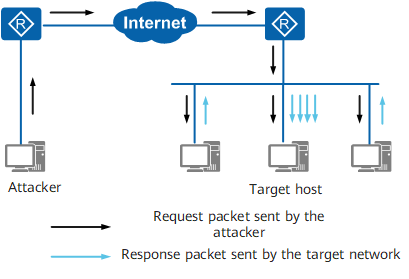
Attack Defense - AR100, AR120, AR150, AR160, AR200, AR1200, AR2200, AR3200, and AR3600 V200R010 CLI-based Configuration Guide - Security - Huawei

Attack Defense - AR100, AR120, AR150, AR160, AR200, AR1200, AR2200, AR3200, and AR3600 V200R010 CLI-based Configuration Guide - Security - Huawei

Detecting UDP-based Amplification Attacks_Security Technologies and Applications_Best Practices_UDP-based Amplification Attack Check_Huawei Cloud
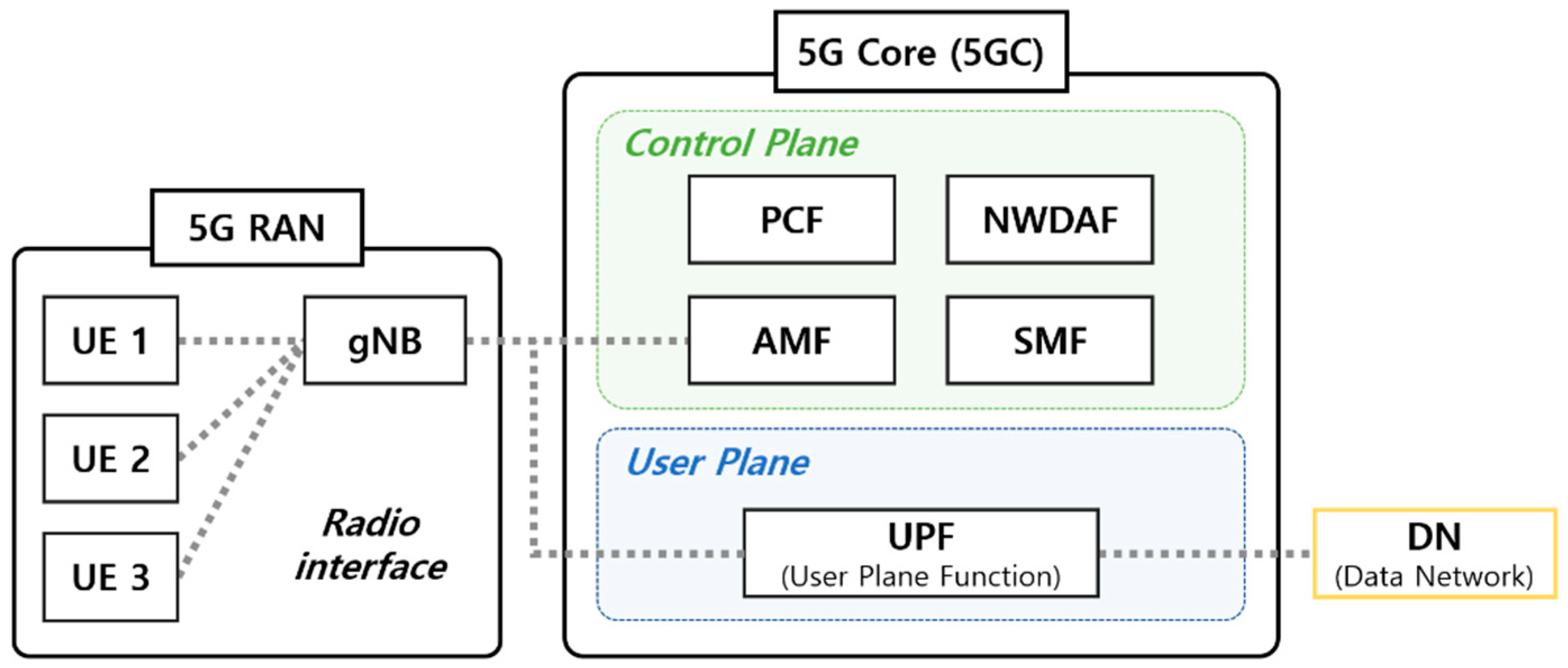
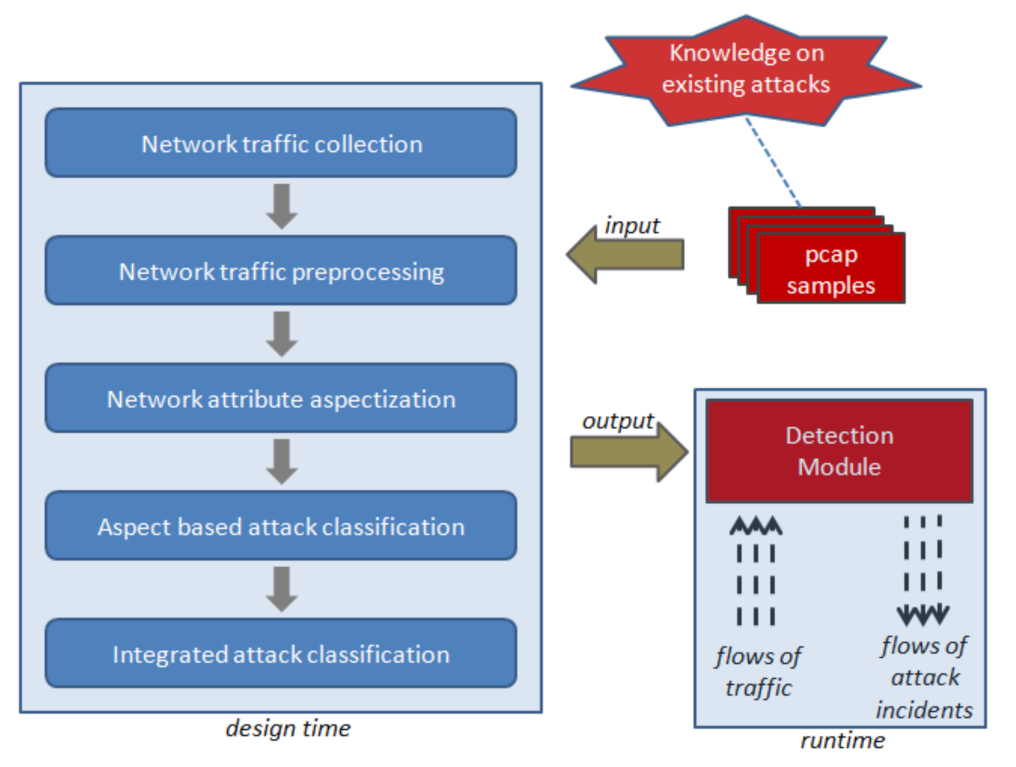
Sensors | Free Full-Text | Effective Feature Selection Methods to Detect IoT DDoS Attack in 5G Core Network

Attack Defense - AR100, AR120, AR150, AR160, AR200, AR1200, AR2200, AR3200, and AR3600 V200R009 CLI-based Configuration Guide - Security - Huawei